In this tutorial i have go to learn what are the top checklist of mysql security so lets follow below i have mentioned security checklist for mysql.
1. Keep your MySQL software up to date.
What is MySQL ?
MySQL is a relational database, which means that it stores data in tables. Tables are made up of rows and columns, and each row represents a single record. Columns represent the different attributes of the record. For example, a table of users might have columns for the user’s name, email address, and password.
Security thread if i ignore updated MySQL
Ignoring updates for MySQL or any software can introduce various security risks. Regularly updating software is a crucial aspect of maintaining a secure system. Here are some security threats you might face if you ignore MySQL updates:
- Security Vulnerabilities:
- Updates often include patches for known security vulnerabilities. Ignoring updates leaves your system exposed to potential exploits that attackers can use to compromise the MySQL server.
- Data Breach:
- Unpatched software can be exploited to gain unauthorized access to your MySQL database, leading to a potential data breach. Regular updates help protect sensitive data stored in your databases.
- Malware and Ransomware:
- Exploits targeting outdated software can lead to the installation of malware or ransomware on your system. Ransomware attacks can encrypt your data and demand payment for its release.
- Denial-of-Service (DoS) Attacks:
- Unpatched servers may be susceptible to denial-of-service attacks, impacting the availability of your MySQL service. Updates often include improvements to mitigate such attacks.
Example :-
sudo apt update
sudo apt upgrade
2. Limit Access to MySQL Server.
Another important security measure is to limit access to your MySQL server. By default, MySQL allows remote connections from any host, which can be a security risk. You should only allow connections from trusted hosts or IP addresses.
To limit access to your MySQL server, you can modify the MySQL configuration file (my.cnf) and add the following line:
cssCopy codebind-address = 127.0.0.1
Next restart the server
sudo service mysql restart
3. Use a web application firewall to protect your MySQL web applications.
What is Firewall and Allow Necessary Ports ?
Enabling a firewall and allowing necessary ports are security measures to control and regulate network traffic to and from your computer or server. Firewalls act as a barrier between your system and the internet or other networks, helping to prevent unauthorized access and securing your system.
Why We need to do this Firewall Ports ?
Enabling a firewall and managing open ports is a crucial aspect of securing your computer or server. Here’s why managing firewall ports is important:
- Security:
- Unauthorized Access Prevention: Firewalls help prevent unauthorized access to your system by blocking incoming connections that are not explicitly allowed.
- Network Segmentation: By controlling which ports are open, you can segment your network and limit exposure to potential security threats.
- Protection Against Exploits:
- Exploit Prevention: Firewalls protect your system from potential exploits and attacks by controlling which services and ports are accessible.
- Controlled Access to Services:
- Service Restriction: You can control which services are accessible from the network. For example, you may allow access to web services (HTTP and HTTPS) but restrict access to certain administrative services.
Security thread if i ignore this Firewall and Allow Necessary Ports ?
If you ignore your firewall and allow necessary ports, you could be putting your system at risk of a number of security threats, including:
- Malware attacks: Malware can exploit open ports to gain access to your system and steal your data, install malware, or launch denial-of-service (DoS) attacks.
- Unauthorized access: Attackers can use open ports to gain unauthorized access to your system and steal your data, or launch attacks against other systems on the network.
- DoS attacks: DoS attacks can overwhelm your system with traffic, making it unavailable to legitimate users.
- Man-in-the-middle attacks: Man-in-the-middle attacks allow attackers to intercept and modify communication between your system and other systems on the network.
Example :-
sudo ufw allow 80
sudo ufw allow 443
sudo ufw enable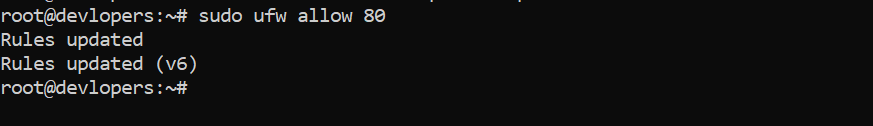
4. Limit the privileges that MySQL users have.
To limit the privileges that MySQL users have, you can use the GRANT statement to assign specific privileges to a user or role. MySQL provides a fine-grained privilege system that allows you to control access to databases, tables, and other resources
5. User Authentication
When databases authorize users for access, the inherent assumption is that the user has already been authenticated and proven their identity. Security best practices require the authentication or identity verification of all types of users such as guests, employees, customers, and administrators. User authentication security sub-categories include insider threat management, user verification, and privileged access management.
- Access MySQL: Open a terminal and log in to MySQL as the root user:
mysql -u root -p2. Create a New User:
Create a new MySQL user with a username and password:
CREATE USER 'your_username'@'localhost' IDENTIFIED BY 'your_password';3. Grant Privileges:
Grant specific privileges to the user. For example, to grant all privileges on a specific database:
GRANT ALL PRIVILEGES ON your_database.* TO 'your_username'@'localhost';After granting privileges, flush the privileges to apply the changes:
FLUSH PRIVILEGES;EXIT;
4. Monitor your MySQL server for suspicious activity
Monitoring your MySQL server for suspicious activity is crucial for identifying potential security threats and taking timely actions to mitigate risks. Here are some steps and tools you can use to monitor MySQL for suspicious activity:
1. MySQL General Query Log:
- Enable the MySQL general query log to record all SQL statements received from clients. Be cautious, as this can generate a large log file:
# Add the following to your my.cnf or my.ini file
[mysqld]
general_log = 1
general_log_file = /path/to/general.log
5. Securing Local and Remote Database Access
1. Log in to MySQL:
mysql -u root -p
2. Set or Change Password:
CREATE USER 'wizbrand_learning'@'localhost' IDENTIFIED BY '8789';
GRANT ALL PRIVILEGES ON *.* TO 'wizbrand_learning'@'localhost';
FLUSH PRIVILEGES;
Security thread if i ignore password for mysql ?
Ignoring or neglecting to set a password for MySQL introduces significant security risks to your database and server. Here are some of the security threats and consequences associated with not having a password for your MySQL database:
- Unauthorized Access:
- Without a password, anyone with access to your server can connect to your MySQL database. This includes malicious actors who may attempt to exploit vulnerabilities or gain unauthorized access to your data.
- Data Breach:
- Lack of authentication allows unauthorized users to read, modify, or delete your database data. This could lead to a data breach, exposing sensitive information and violating privacy regulations.
- Database Manipulation:
- An attacker could modify or delete your database records, disrupting your application’s functionality or causing data loss.
6. Enable Network Security
Restrict access to your MySQL server by allowing connections only from trusted IP addresses. Use firewall rules or the bind-address directive in your MySQL configuration file to limit access. Additionally, consider running your MySQL server on a non-default port to reduce the risk of automated attacks.
To change the bind-address and port of the MySQL server, you need to edit the MySQL configuration file. The MySQL configuration file is typically located at
/etc/mysql/mysql.cnfTo edit the MySQL configuration file, use a text editor such as nano or vim. For example, to edit the MySQL configuration file using nano, run the following command:
Example :-
[mysqld]
bind-address = 192.168.1.100
port = 33077. Secure Against Attackers
To make a MySQL system secure, you should maintain the following suggestions :
- Require all MySQL accounts to have a password.
- Make sure that the only Unix user account with read or write privileges in the database directories is the account that is used for running mysqld.
- Never run the MySQL server as the Unix root user
- Do not grant the FILE privilege to nonadministrative users
- Do not permit the use of symlinks to tables.
- Stored programs and views should be written using the security guidelines
- If you do not trust your DNS, you should use IP addresses rather than hostnames in the grant tables.
- If you want to restrict the number of connections permitted to a single account, you can do so by setting the max_user_connections variable in mysqld.
8. Granting Privileges to User in MysQL
There are multiple types of privileges that can be granted to a user account.
Example :-
Grant All Privileges on a Specific Database:
Suppose you want to grant all privileges to a user named your_user on a database named your_database. The syntax for granting all privileges on a specific database is as follows:
GRANT ALL PRIVILEGES ON your_database.* TO 'your_user'@'localhost' IDENTIFIED BY 'your_password';
Grant All Privileges on All Databases:
If you want to grant all privileges to a user on all databases, you can use the wildcard * for the database name:
GRANT ALL PRIVILEGES ON *.* TO 'your_user'@'localhost' IDENTIFIED BY 'your_password';
Security thread if i ignore Privileges
Ignoring privileges and not properly managing user privileges in MySQL can lead to significant security threats. Properly assigning and managing privileges is a crucial aspect of securing your MySQL database. Here are some security risks and considerations if you ignore privileges in MySQL:
- Unauthorized Access:
- Ignoring privileges may result in granting overly broad access to users. This could lead to unauthorized users gaining access to sensitive data or making unintended modifications to the database.
- Data Exposure:
- Users with excessive privileges may have access to confidential or sensitive information, leading to data exposure and potential breaches.
- Data Manipulation:
- Users with excessive privileges can modify or delete data, impacting the integrity of the database. This could result in data loss or unauthorized changes.
- Security Principle Violation:
- Ignoring the principle of least privilege violates a fundamental security principle. Users should only be given the minimum level of access necessary to perform their tasks.
- SQL Injection Exploitation:
- Without proper privilege management, SQL injection vulnerabilities become more severe. An attacker might exploit injection vulnerabilities to gain unauthorized access or manipulate data.